I am trying to gather some freely available tools, techniques and links that can help running SSL/TLS related tests. The more I learn, the more stuff I will add. SSL/TLS is not that simple, you cannot rely on the output of just 1 tool. You also need to understand how that tool/script works internally.
1. Nmap ssl-enum-ciphers script
http://nmap.org/nsedoc/scripts/ssl-enum-ciphers.html
2. sslscan. (based on openssl)
http://sourceforge.net/projects/sslscan/
Uses openssl internally. If you compile it on redhat, you may run into compilation issues because EC crypto is not there in openssl in redhat (depending on your version). If you are not interested in testing EC, then you can comment out the lines as mentioned in my previous post:
http://rhosted.blogspot.in/2014/02/using-sslscan-and-ssltests-for-testing.html
3. ssl_tests (based on sslscan/openssl)
ssl_tests is a shell script that uses sslscan and openssl internally to connect.
www.pentesterscripting.com/discovery/ssl_tests
4. Using OpenSSL directly
5. sslyze
root@kali:~# sslyze --tlsv1 www.example.com
6. TestSSLServer : A simple java program that does the same kind of testing. The program uses plain sockets and raw packet level inspection and does not depend on any provider like JSSE or Openssl as such. So it is very good for learning at raw packet level as to how do you know whether compression is supported or not. The program also checks CRIME and BEAST status by checking the compression support in the connection and inspecting the protocol version. You can see how it does that in the comments.
However, I would recommend you develop your own understand about CRIME/BEAST working and its latest status depending on your own application implementation rather than relying on the output of the testing program. Things and assumptions keep changing with time.
http://www.bolet.org/TestSSLServer/
Original reference: http://security.stackexchange.com/questions/20376/tools-to-test-for-beast-crime-that-arent-internet-based
Here is a screenshot of running the tool using eclipse:
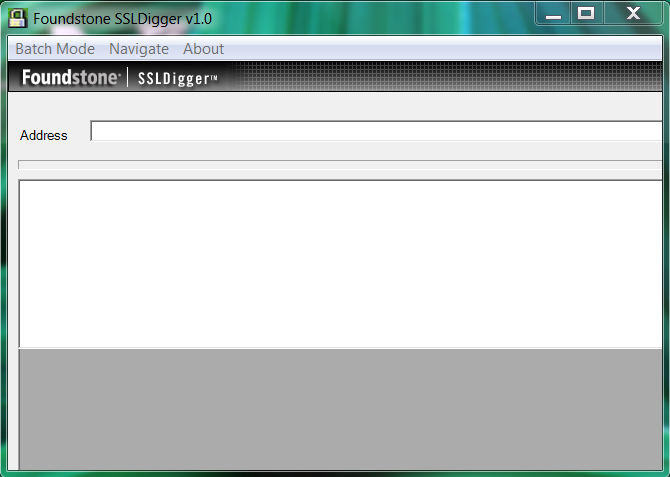
7. SSLDigger by Foundstone -
It is a windows based tool. However, it does not have support for a lot of latest ciphers probably because it has not been updated.
http://www.mcafee.com/uk/downloads/free-tools/ssldigger.aspx
8. If you want to play around writing your own tool, here is a small test I did in Java. This tool is an example of how you can use a crypto library for SSL testing. The drawback is that you can only test the cipher that your client library supports. In contrast to TestSSLServer (6) which does a packet level inspection and does not rely on a local crypto library.
http://rhosted.blogspot.in/2014/08/jsse-based-ssl-ciphersuite-tester.html
9. Testing the SSL for mysql and postgresql?
Databases do not really follow the procedures of a typical SSL/TLS handshake. You need to have a db client for that or you can use wireshark. Wanna see an example, check my earlier notes on mysql's ssl:
http://rhosted.blogspot.in/2014/10/mysql-tlsv1-capture-using-wireshark.html
10. SSLAudit - https://code.google.com/p/sslaudit/
I found SSLAudit pretty good.
11. SSL Breacher
http://bl0g.yehg.net/2014/07/ssl-breacher-yet-another-ssl-test-tool.html
12. TLSSLed (Based on sslscan/openssl)
http://blog.taddong.com/2011/05/tlssled-v10.html
To be continued..
https://www.openssl.org/docs/apps/ciphers.html#EXAMPLES
[*] A little advanced but good learning material about TLS
https://www.owasp.org/index.php/Transport_Layer_Protection_Cheat_Sheet
[*] Explains a lot of common SSL problems in a very simple way.
https://www.howsmyssl.com/s/about.html
[*] Understanding the meaning of a cipher string like DHE-RSA-AES256-SHA
http://nzbget.net/Choosing_a_cipher
[*] High/Low/Med grade ciphers
https://bto.bluecoat.com/packetguide/appcelera-3.0.2/configure/ssl-cipher-details-popup.htm
https://kb.berkeley.edu/page.php?id=23113
Tools and scripts (will keep adding)
Testing might be affected with what openssl version you have installed, because older versions may not have support for newer cipher suites or higher protocols. So while testing you need to take this into consideration.
nmap --script ssl-enum-ciphers -p 443 hostname
http://nmap.org/nsedoc/scripts/ssl-enum-ciphers.html
2. sslscan. (based on openssl)
http://sourceforge.net/projects/sslscan/
Uses openssl internally. If you compile it on redhat, you may run into compilation issues because EC crypto is not there in openssl in redhat (depending on your version). If you are not interested in testing EC, then you can comment out the lines as mentioned in my previous post:
http://rhosted.blogspot.in/2014/02/using-sslscan-and-ssltests-for-testing.html
3. ssl_tests (based on sslscan/openssl)
ssl_tests is a shell script that uses sslscan and openssl internally to connect.
www.pentesterscripting.com/discovery/ssl_tests
4. Using OpenSSL directly
openssl s_client -connect host:port
5. sslyze
root@kali:~# sslyze --tlsv1 www.example.com
6. TestSSLServer : A simple java program that does the same kind of testing. The program uses plain sockets and raw packet level inspection and does not depend on any provider like JSSE or Openssl as such. So it is very good for learning at raw packet level as to how do you know whether compression is supported or not. The program also checks CRIME and BEAST status by checking the compression support in the connection and inspecting the protocol version. You can see how it does that in the comments.
However, I would recommend you develop your own understand about CRIME/BEAST working and its latest status depending on your own application implementation rather than relying on the output of the testing program. Things and assumptions keep changing with time.
http://www.bolet.org/TestSSLServer/
Original reference: http://security.stackexchange.com/questions/20376/tools-to-test-for-beast-crime-that-arent-internet-based
Here is a screenshot of running the tool using eclipse:
7. SSLDigger by Foundstone -
It is a windows based tool. However, it does not have support for a lot of latest ciphers probably because it has not been updated.
http://www.mcafee.com/uk/downloads/free-tools/ssldigger.aspx
9. Testing the SSL for mysql and postgresql?
Databases do not really follow the procedures of a typical SSL/TLS handshake. You need to have a db client for that or you can use wireshark. Wanna see an example, check my earlier notes on mysql's ssl:
http://rhosted.blogspot.in/2014/10/mysql-tlsv1-capture-using-wireshark.html
10. SSLAudit - https://code.google.com/p/sslaudit/
I found SSLAudit pretty good.
11. SSL Breacher
http://bl0g.yehg.net/2014/07/ssl-breacher-yet-another-ssl-test-tool.html
12. TLSSLed (Based on sslscan/openssl)
http://blog.taddong.com/2011/05/tlssled-v10.html
To be continued..
Helpful references for testing
- http://superuser.com/questions/109213/is-there-a-tool-that-can-test-what-ssl-tls-cipher-suites-a-particular-website-of
- https://www.owasp.org/index.php/Testing_for_SSL-TLS_%28OWASP-CM-001%29
- https://www.owasp.org/index.php/Testing_for_Weak_SSL/TLS_Ciphers,_Insufficient_Transport_Layer_Protection_%28OTG-CRYPST-001%29
- More about secure socket implementation in Java:
http://download.java.net/jdk7/archive/b123/docs/api/javax/net/ssl/SSLSocket.html
TLS learning
[*] Listing of Openssl ciphers (meaning of examples like ALL:!ADH:@STRENGTH)https://www.openssl.org/docs/apps/ciphers.html#EXAMPLES
[*] A little advanced but good learning material about TLS
https://www.owasp.org/index.php/Transport_Layer_Protection_Cheat_Sheet
[*] Explains a lot of common SSL problems in a very simple way.
https://www.howsmyssl.com/s/about.html
[*] Understanding the meaning of a cipher string like DHE-RSA-AES256-SHA
http://nzbget.net/Choosing_a_cipher
[*] High/Low/Med grade ciphers
https://bto.bluecoat.com/packetguide/appcelera-3.0.2/configure/ssl-cipher-details-popup.htm
SSL/TLS best practices
[*] https://www.ssllabs.com/projects/best-practices/index.htmlProducts using SSL
[*] Postgres using SSL (How to test SSL being used)https://kb.berkeley.edu/page.php?id=23113







No comments:
Post a Comment